Audits aren’t fun. However, they play a critical role in ensuring accountability and compliance across a broad range of important standards. Chief among those is the SOC 2 audit. According to the AICPA:
These reports are intended to meet the needs of a broad range of users that need detailed information and assurance about the controls at a service organization relevant to security, availability, and processing integrity of the systems the service organization uses to process users’ data and the confidentiality and privacy of the information processed by these systems. These reports can play an important role in:
- Oversight of the organization
- Vendor management programs
- Internal corporate governance and risk management processes
- Regulatory oversight [1]
This report is important to instill security and controls throughout the organization and to give your customers, partners, and vendors peace of mind.
The SOC 2 Controls List
Simply put, SOC 2 Controls List refers to a comprehensive set of policies, procedures, and practices put in place to ensure the security, availability, processing integrity, confidentiality, and privacy of customers’ data.
These controls, which align with the Trust Services Criteria, serve as a basis for evaluating and reporting on the effectiveness of an organization’s information systems in a SOC 2 audit.
Control Data For Your SOC 2 Audit
A key ingredient to a SOC 2 certification is proof. Simply promising adherence to controls isn’t enough. When we first underwent our SOC 2 Type II Audit as a small team of just ten employees, we found our own product, Torii, to be immensely useful in helping to gather and store the proof we needed.
There is a lot of preparation that goes into SOC 2 report. and Torii can help reduce the workload across teams. Here are the best practices for using Torii to help prepare for your SOC 2.
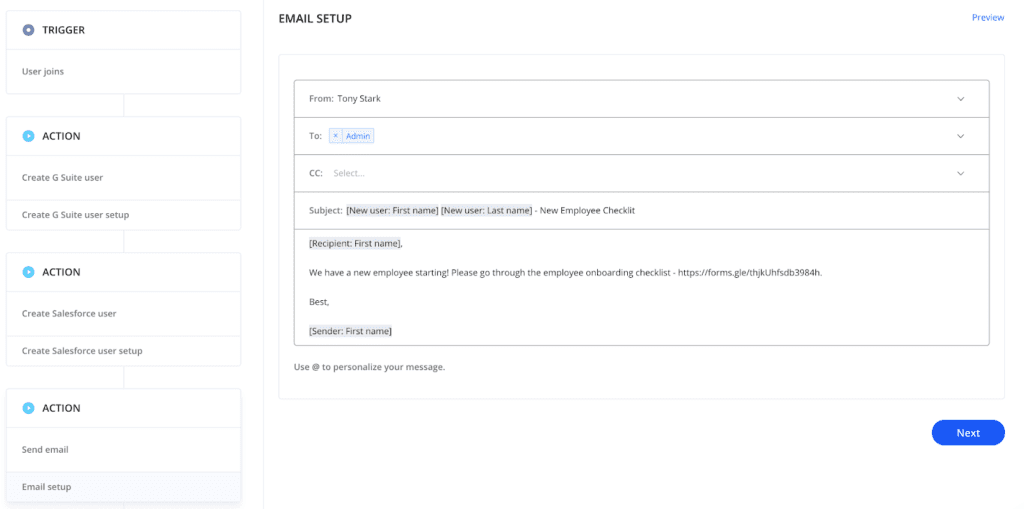
1. Gather Onboarding Data for New Employees
Torii can be used to create and manage the onboarding process of new employees. Not only can you automatically add users to your core tools before their first day, but you can also do the following:
- Alert appropriate teams that a new employee is starting automatically
- Send a checklist of steps that need to be taken for the employee
- Send a checklist of steps that need to be taken by the employee
- Send employee responsibilities and company policies to the employee
- Add employees to user groups on different systems automatically
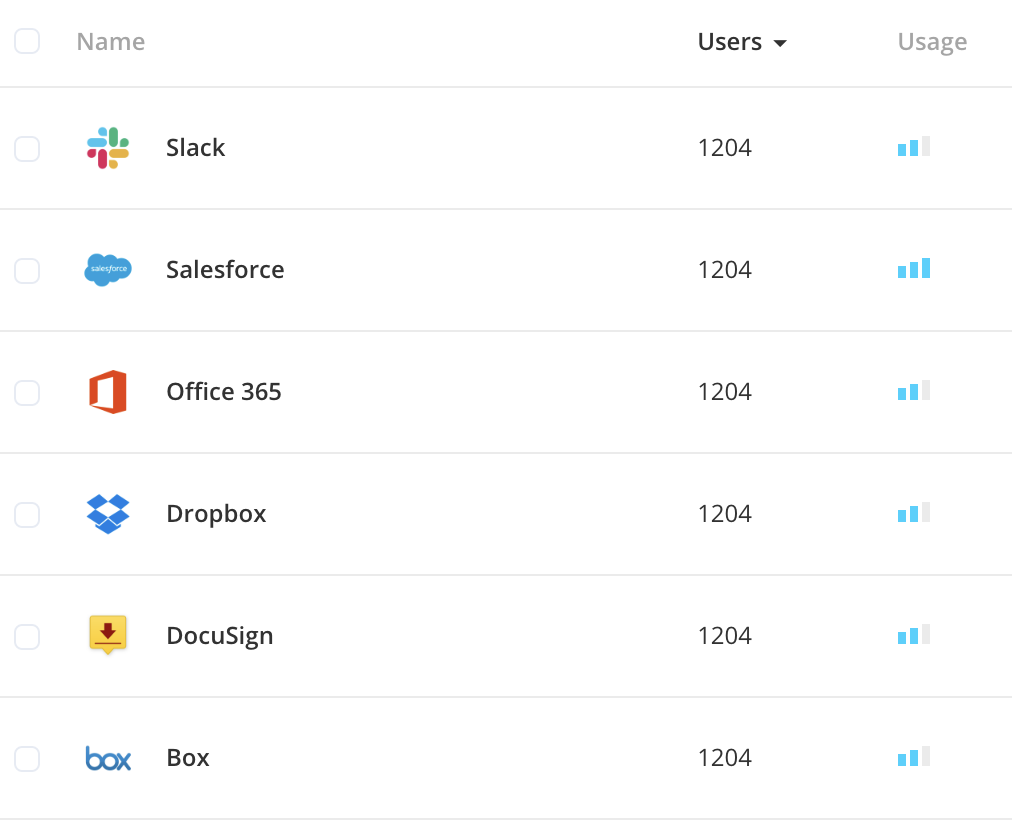
2. Conduct Annual Access Review
Torii provides you with a real-time view of what systems employees are using from the moment they join the company until the time they leave. For your core tools, you can use Torii to not only see who is a current and active user but also what access rights they have. This allows you to do the following:
- Remove users who no longer need access to the application
- Remove admin rights to users who no longer need privileged access
- Add users and admins who should have access to the application
- Set up an automated workflow to send alerts whenever an employee accesses a retired application
- Using our SSO audit report, you can review what method employees are using to sign up for the different systems.
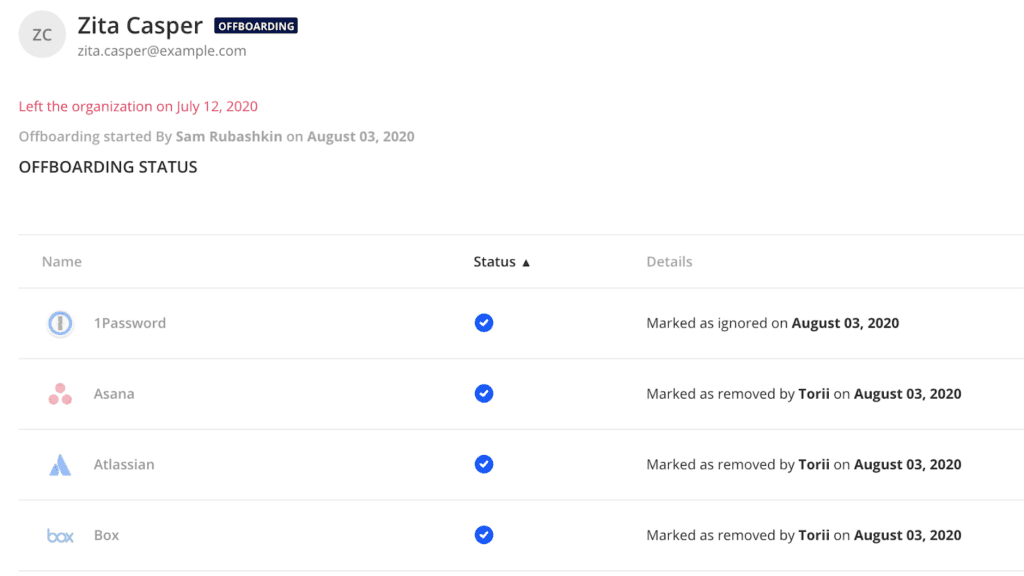
3. Fully Offboard Terminated Employees
Torii can be used to create and manage the offboarding process. In addition to automatically offboarding employees from core tools, you can do the following:
- Send automated alerts to remove the employee from all applications
- Send automated alerts to employees responsible for none SaaS application tasks
- Automatically transfer files from one employee to another as part your onboarding process
- Real-time report and audit of the offboarding process of each employee
4. Uplevel Vendor Management
Torii helps with several aspects of vendor management. You can store all relevant information (e.g., contracts, contacts, use cases) and manage the renewal. You will receive notifications when renewals are upcoming so you can begin your security process. If you will be ending a relationship with a vendor, you can close this application within Torii and keep all data for historical and audit purposes.
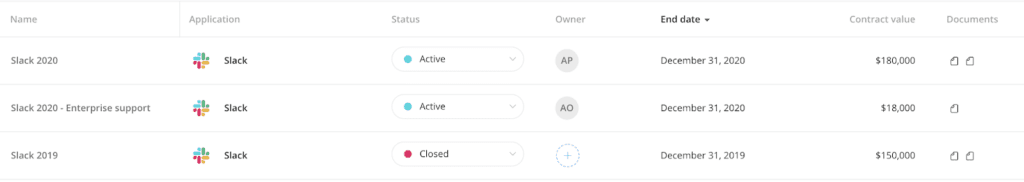
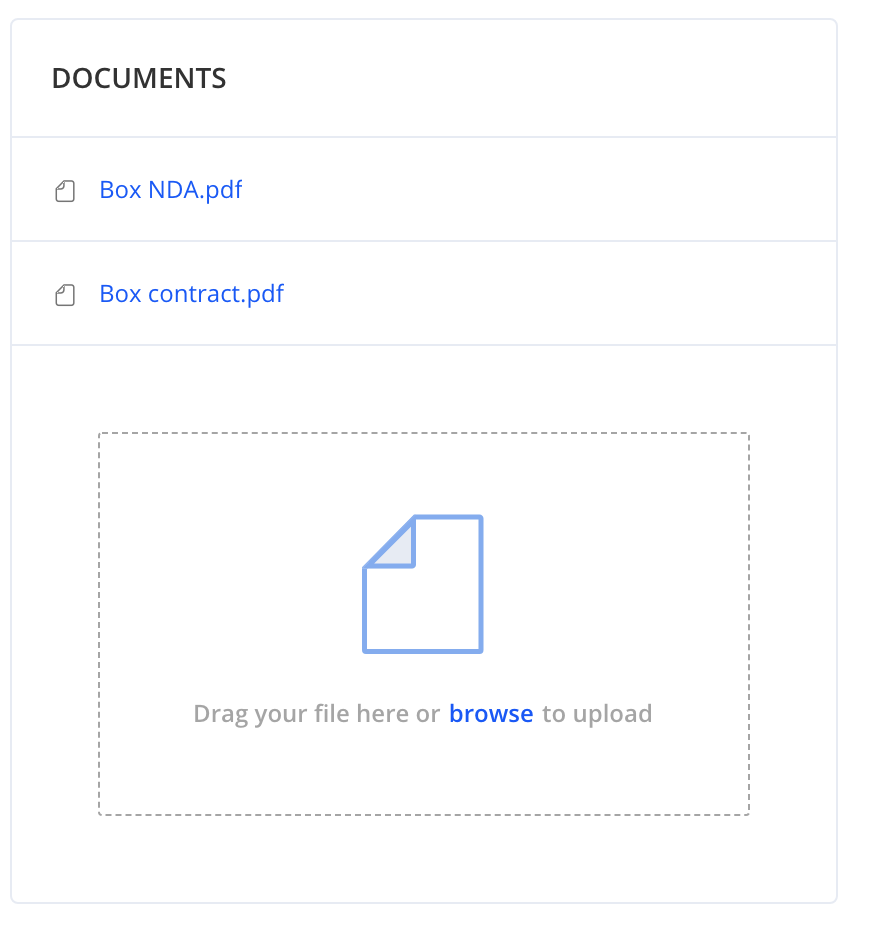
5. Stash Confidentiality Agreements with Vendors
You will need to ensure that your vendors have the same level of confidentiality commitments as you do. This can include signing NDAs and DPAs.
Store all of these documents, at the application level, for easy storage and access across all teams.
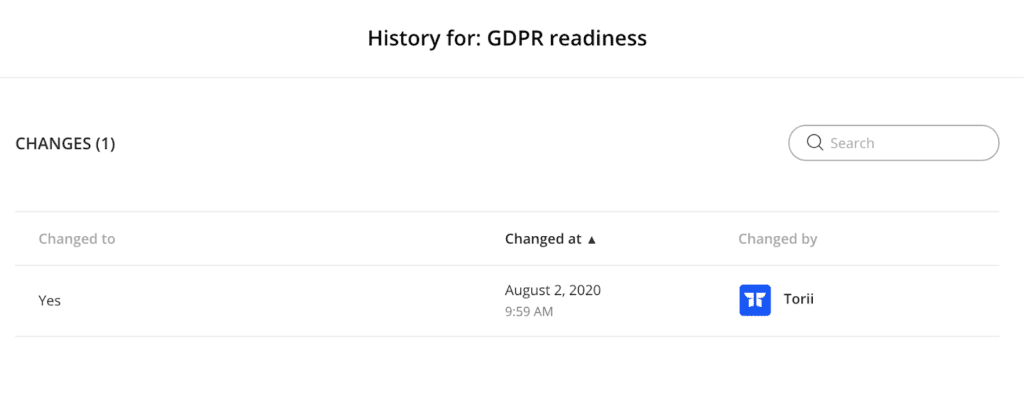
6. Keep an Audit Trail
Having the controls in place is part of the battle. Being able to audit your work and prove the controls are working is just as essential. Any automated work completed by Torii and updates made within the platform is kept for this purpose. You will have access to the following:
- Who was onboarded, and what actions were taken
- Who was offboarded, and what actions were taken
- All applications discovered
- All documents stored
- All information added, including who changed them and when
7. Store Data for Easy Use and Discovery
Torii can be your Source of Truth for all SaaS applications. Having a one-stop shop for all this information increases visibility across the organization and saves time in finding important documentation. This is incredibly valuable when preparing for your SOC 2.
Planning for the Next Annual Review
These reports will be needed every 6 to 12 months. Having the right tool to gather, maintain and share your data is key to completing SOC 2 as efficiently as possible. If you would like to discuss further how Torii can help with your SOC 2 preparation please reach out to your CSM or [email protected]
[1] SOC 2® – SOC for Service Organizations: Trust Services Criteria: https://www.aicpa.org/interestareas/frc/assuranceadvisoryservices/aicpasoc2report.html

